Effortlessly Co-create, Refine, and Finalize Data With Colleagues and Third Parties
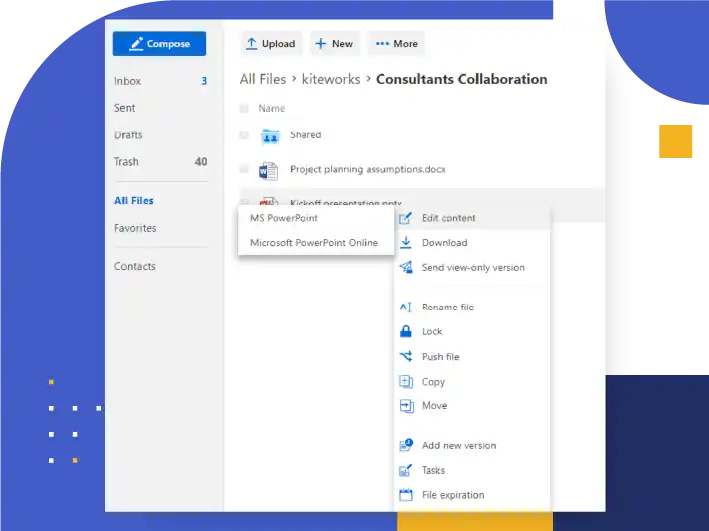
Co-Authoring | Secure Collaboration
- Multiple web users seamlessly edit in real time in Microsoft Office Online
- Power users enjoy the full functionality of Microsoft Office on the desktop without overwrite risks
- Mobile users automatically edit in Microsoft Office
- Users of specialized non-Office editors simply drag-and-drop new versions without overwriting others’ work
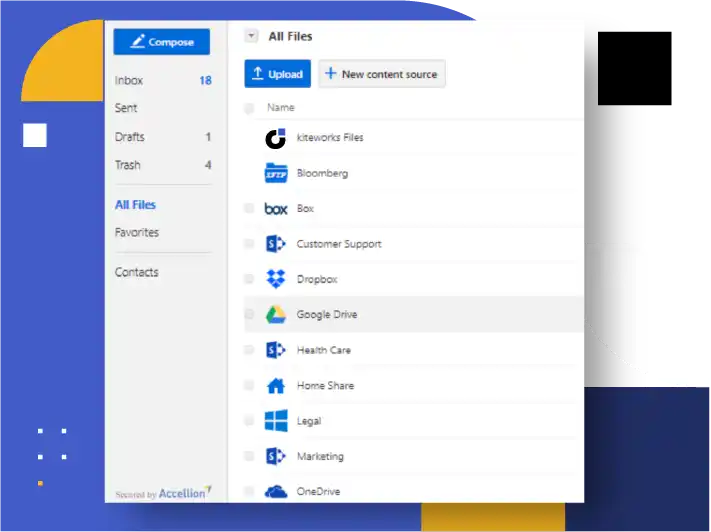
Maximize Editing Productivity on Any Data From Anywhere, on Any App, with Any Device
Universal | Secure Collaboration
- Employees invite third parties to collaborate securely anywhere across the internet
- Employees securely collaborate with third parties using enterprise data, automatically accessing, versioning, and protecting source enterprise repositories
- Users collaborate securely from wherever they work, whether a browser, mobile device, or enterprise app such as Microsoft Office, Salesforce or iManage
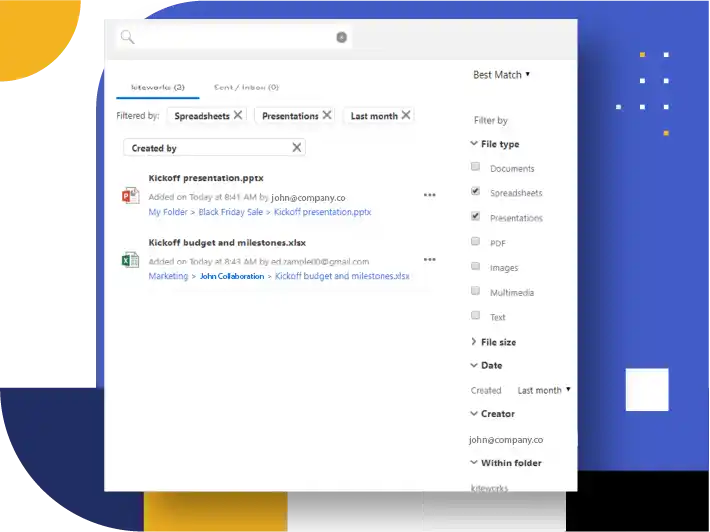
Provide the Tools That Make Collaboration Effective
Tools | Secure Collaboration
- Each saved change creates a new, tracked, auditable version, and end users can even roll it back when necessary
- Users give each other feedback on documents using comments
- Users subscribe to notifications of new versions and comments
- Users run full text searches to find any document to which they have access privileges
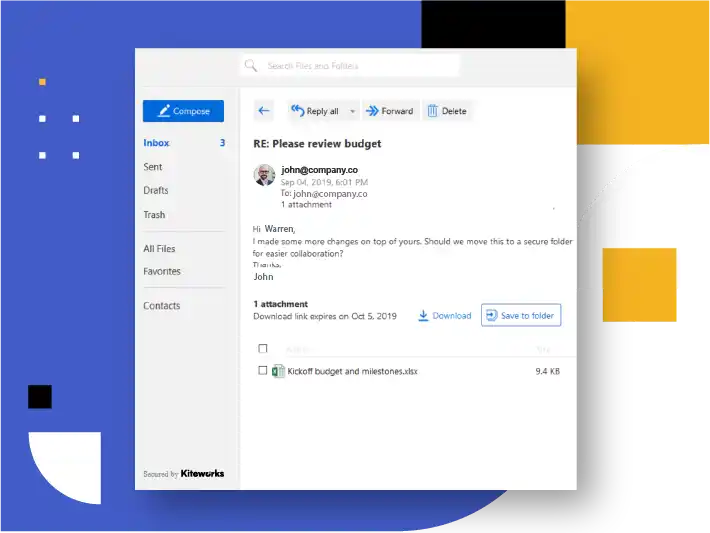
Embrace Email Collaboration
Email | Secure Collaboration
- Real-world collaboration often starts with an email, an attachment and multiple replies
- Move seamlessly from a secure email thread to a secure shared folder when it suits the users
- Invite more users to the collaboration folder, with appropriate permissions and restrictions based on their need to edit, download, or know the information
- Email the resulting final version to other parties as a secure attachment
- Follow a clear audit trail and versioning of the entire process
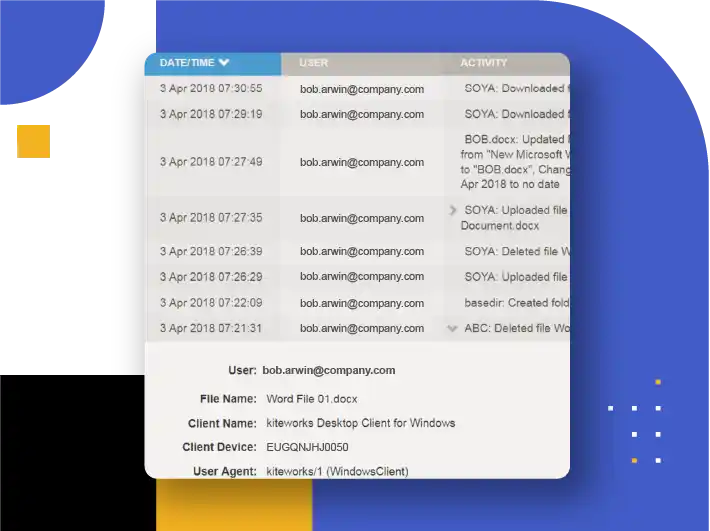
Prevent Breaches and Compliance Fines from Inadvertent and Intentional Leaks
Security and Governance | Secure Collaboration
- Reduce risks of inadvertent sharing outside the organization with the Kiteworks platform’s role-based permissions and least privilege defaults
- Protect data with granular access controls, such as watermarked-view-only privileges and expiration policies
- Satisfy security controls with hardened virtual appliance and strong encryption in transit and at rest
- Automatically quarantine incoming malware and block leaks of IP, PII, and PHI
- Leverage the complete audit trail and logging for compliance reporting and threat analytics
FEATURED RESOURCES
Customer Use Cases: Kiteworks Private Content Network Innovations


Customer Use Cases: Kiteworks Private Content Network Innovations
SafeEDIT Next-Gen DRM Maximizes Productivity and Security